Contact Search Resource Guide Free Phone Number Lookup Revealing Caller Discovery Tools
The guide surveys how free phone-number lookups assemble data from public records, carrier signals, and crowd contributions to reveal caller identities. It remains analytic about reliability, noting potential privacy risks and the need for consent. Skepticism is applied to dubious registries and paywalls, with emphasis on reproducible methods and transparent data sources. The discussion still leaves open questions about accuracy, verification, and the boundaries of lawful use, inviting further scrutiny and careful consideration of safeguards.
What Is Free Phone Number Lookup and Why It Helps
Free phone number lookup refers to services that identify the owner or associated details of a telephone number by querying public records, carrier data, and crowdsourced contributions. The practice offers practical visibility but invites concern about data provenance and consent. It clarifies privacy basics and challenges lookup myths, prompting measured evaluation of accuracy, limits, and potential misuse in a freedom-focused information landscape.
Reputable Free Tools for Caller Discovery
Reputable free tools for caller discovery are evaluated here through objective criteria, separating accuracy, privacy implications, and usability from hype. The analysis emphasizes calling patterns, transparent data sources, and reproducible results, while highlighting privacy safeguards and consent considerations. Enhanced caller IDs may improve context but require critical assessment against misuse; scam prevention depends on timely updates and credible incident reporting, not sensational claims or opaque algorithms.
How to Verify Numbers and Protect Privacy
This section examines practical methods for verifying phone numbers while protecting personal privacy, emphasizing verifiable data sources, consent considerations, and minimal data exposure. It remains analytical and skeptical, outlining reliable verification methods and cautioning against dubious registries. Privacy safeguards are essential, ensuring data minimization and transparent use. Ultimately, prudent verification relies on consent, verifiable records, and disciplined information handling.
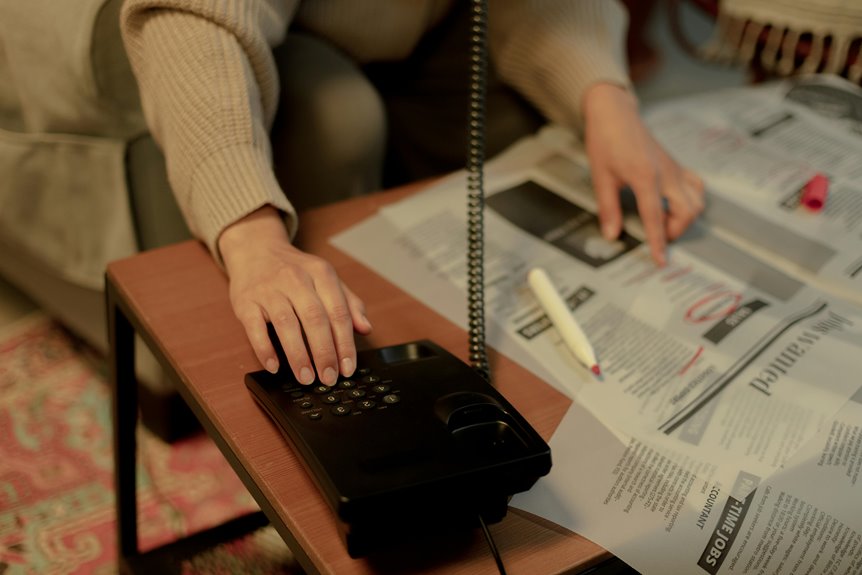
Step-By-Step Workflow to Identify Missed Calls Without Paywalls
Identifying missed calls without paywalls requires a structured, data-driven workflow that minimizes reliance on paid services. The missed calls workflow prioritizes verifiable data points, timing patterns, and cross-checking sources, avoiding assumptions. Analysts contrast results with baseline norms, scrutinizing caller discovery basics, consent considerations, and privacy implications. Outputs emphasize reproducibility, transparency, and skepticism toward unverifiable anecdotes, ensuring freedom through rigorous, independent verification.
Conclusion
This analysis remains analytical, skeptical, precise, and cautious. It emphasizes verification, verification, verification; it emphasizes transparency, transparency, transparency. It weighs data sources, data quality, data minimization; it weighs data sources, data quality, data minimization. It promotes consent, consent, consent; it promotes consent, consent, consent. It highlights reproducible workflows, reproducible workflows, reproducible workflows; it highlights reproducible workflows, reproducible workflows, reproducible workflows. It calls for accountability, accountability, accountability; it calls for accountability, accountability, accountability; and it urges prudent use, prudent use, prudent use.
